In the contemporary digital era, where technology is intertwined with our daily lives, the threat of cyber-attacks, particularly ransomware, is more prevalent than ever. Ransomware, malicious software designed to encrypt user data and demand payment for its release, has evolved significantly over the years, posing a severe threat to individuals and organizations alike. This guide delves into the definition, evolution, impact, and future ransomware trends, providing insights into the sophisticated nature of such attacks and the imperative need for robust cybersecurity measures.
It additionally describes preemptive tactics and recommended approaches for reducing the vulnerability to ransomware incidents while ensuring the protection of digital resources.
Ransomware Defined
Ransomware is a distinct form of malicious software, often referred to as malware, with the explicit purpose of blocking access to computer systems or data, effectively keeping them in a state of captivity until a designated ransom is paid to its originator. This vindictive software achieves this by encrypting the user’s data, making it inaccessible, and then demanding payment, for the decryption key needed to restore access.
The cunning nature of ransomware often lies in its disguise as a legitimate or harmless file, which unsuspecting users are lured into downloading or opening, commonly through seemingly innocent email attachments or links. Once activated, the ransomware infiltrates the system, locking users out of their files or entire system.
Ransomware does not discriminate in its targets, posing a threat to individuals and businesses alike. For individuals, it can mean the loss of access to personal files and data, while companies may experience significant disruption in operations, compromise of sensitive data, and substantial financial losses due to downtime and ransom payments.
The evolution of ransomware has made it increasingly sophisticated, employing advanced encryption algorithms and evasion techniques to bypass security measures. It is a continually evolving and persistent threat in the cyber landscape. The repercussions of a ransomware attack can have broad-reaching effects, highlighting the critical need for heightened vigilance, robust cybersecurity procedures, and proactive defensive strategies to lower the risk of infection and safeguard digital assets.

The Early Years of Ransomware & Its Evolution Over the Years
The Current State of Ransomware

The Impact of Ransomware Evolution on IT Operations
Increasing Cost of Recovery
Enhanced Business Disruption
Heightened Security Measures
The persistent threat of sophisticated ransomware attacks has implemented advanced and robust cybersecurity solutions imperative. Organizations must invest in real-time threat intelligence and behavior-based detection systems to effectively counter the evolving ransomware threats.
Increased Complexity in IT Operations
Shift in IT Priorities
Change in Backup and Recovery Strategies
The evolution of ransomware necessitates adopting more sophisticated and comprehensive backup solutions to ensure data integrity and availability post-attack. Traditional backup systems are often inadequate against modern ransomware, emphasizing the need for innovative recovery strategies.
Increased Demand for Cyber Insurance
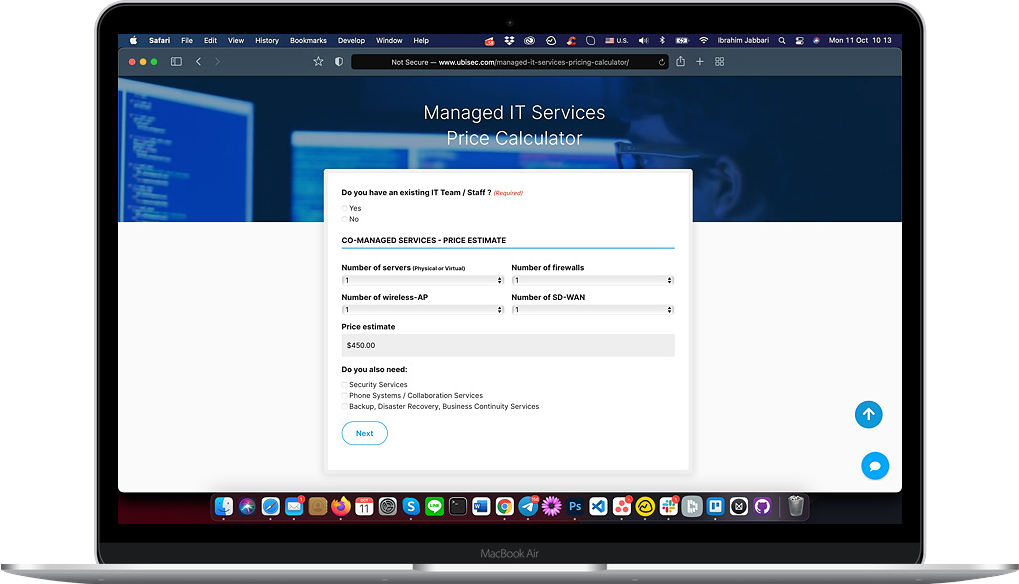
Are you unsure about the state of your organization’s cyber hygiene? Click here to take our cybersecurity posture assessment quiz!
Preparing for the Future: Projected Ransomware Trends
Increased Dependence on AI and ML
The future landscape of ransomware will likely see cybercriminals exploiting Artificial Intelligence (AI) and Machine Learning (ML) to devise more sophisticated and adaptive ransomware attacks, automating the identification of vulnerabilities and enhancing the malware’s evasion capabilities.
Rise in RaaS
The widespread adoption of Ransomware-as-a-Service (RaaS) models empowers individuals with limited technical expertise to execute advanced ransomware attacks, expanding the range and variety of potential threats and wrongdoers.
Targeting of IoT Devices
The ubiquitous adoption of Internet of Things (IoT) devices, often characterized by inadequate security measures, presents an attractive target for ransomware attacks, potentially compromising a myriad of connected devices and networks.
Increase in Double Extortion Ransomware Attacks
More Advanced Evasion Techniques
Anticipated advancements in ransomware are expected to employ sophisticated evasion techniques, challenging IT operations to detect and counteract attacks effectively. Utilizing polymorphic code and other advanced methodologies will necessitate continual advancements in defensive cybersecurity measures.

Proactive Measures for IT Operations
Regular Software Updates and Patching
Ensuring software is regularly updated and patched is crucial as outdated software presents exploitable vulnerabilities often targeted by ransomware, emphasizing the importance of maintaining up-to-date security postures.
Employee Training
Comprehensive employee training on the risks associated with ransomware and identifying potential threats is pivotal in fortifying the first line of defense against cyber-attacks and reducing the likelihood of successful infiltrations.
Implementing Multi-factor Authentication
Regular Backups
It’s vital to initiate consistent and regular backups of essential data. These backups act as a safeguard, restoring compromised data with minimal loss and downtime during a ransomware attack.
Incident Response Plan
A meticulously documented and rigorously tested incident response plan is instrumental in swiftly identifying, containing, and eradicating ransomware attacks, minimizing their operational and financial impact.
Advanced Threat Detection Systems
Network Segmentation
Using Antivirus and Antimalware Solutions
Regular Vulnerability Assessment and Penetration Testing
Limiting User Access Rights
Conclusion
Ransomware has come a long way since its inception in the late 1980s, transforming into a sophisticated and formidable threat in the cyber landscape. The evolution of ransomware has been marked by increased complexity, advanced encryption algorithms, and innovative evasion techniques targeting individuals, businesses, and critical infrastructures globally. The alarming surge in ransomware attacks in recent years underscores the need for heightened awareness, advanced cybersecurity solutions, and proactive defense strategies. By understanding the evolving nature of ransomware and implementing comprehensive security measures, you can effectively safeguard your digital assets against the burgeoning spectrum of cyber threats.
Amid rising ransomware threats, it’s vital to stay informed and proactively enhance cybersecurity. Count on Ubisec Systems for expert guidance and innovative solutions. Contact us here today to fortify your defenses and create a secure digital environment for your organization.