In cybersecurity, spear phishing emerges as a sophisticated cyber threat that spans many industries, leaving no facet of the business world untouched. The repercussions of this malicious technique vary significantly among these sectors, hinging on the distinctive character and significance of the data they possess. This exploration examines how spear phishing exerts its influence on diverse sectors, ranging from financial services to manufacturing and encompassing government agencies to the real estate domain. This analysis will also unveil real-world instances of spear phishing attacks, explain the indispensable role of IT operations and support in thwarting such threats, and enumerate practical measures organizations can adopt to fortify their defenses. In a landscape where the battleground of cybersecurity is in perpetual flux, grasping the nuanced implications of spear phishing remains crucial for preserving sensitive information and upholding organizational integrity in the digital era.

Understanding Spear Phishing
Amidst the ever-evolving landscape of cyber threats, Spear phishing emerges as a particularly deceitful and personalized form of attack. Distinguished by its precision and specificity, spear phishing sets itself apart from conventional phishing attempts. In this scheme, cybercriminals painstakingly compose emails that resemble legitimate correspondence from trusted sources, such as banks or colleagues. These deceptive messages are selectively dispatched to specific individuals or organizations with a clear-cut objective: to dupe the recipient into divulging sensitive information, engaging with a malicious link, or unwittingly opening a compromised attachment.
What sets spear phishing apart from its generic counterpart is its adept utilization of personal information concerning the target. This wealth of knowledge about the victim allows the perpetrators to fashion persuasive emails, heightening the likelihood of a successful breach. In this arena, the attackers’ familiarity with particulars such as the target’s name, job title, and professional relationships proves pivotal in crafting these deceitful messages.

How Spear Phishing Attacks Affect Different Sectors
Spear phishing affects various sectors differently due to the nature and value of the information available.
Financial Services
The financial sector suffers tremendously due to unauthorized access to sensitive data through spear phishing. Sensitive data such as account numbers, credit card information, and client details are attractive commodities to threat actors. Any compromise of the security of this data may lead to substantial financial losses, disrupted operations, and a loss of customer trust, tarnishing the reputation of institutions and eroding client confidence.
Manufacturing & Wholesale
The manufacturing and wholesale sectors are lucrative for attackers seeking intellectual property and supply chain information. The repercussions of a successful spear-phishing attack here could lead to a loss of trade secrets, production disruptions, and compromised business relationships, impacting companies’ competitive edge.
Real Estate
Given the high-value transactions involved in real estate, it offers potential high returns for successful spear-phishing attacks. The sector’s handling of sensitive client information makes it particularly attractive to cybercriminals seeking to exploit valuable data for financial gain. Real estate professionals handle sensitive client information, including personal identification, financial records, and transaction details.
Cybercriminals understand that this data holds value, as it can be employed for identity theft, financial fraud, or even be traded on the dark web. The potential harm to individuals and the reputation of real estate firms is substantial if such data is compromised.
Government
Government agencies are treasure troves of sensitive and classified information, making them prime targets for spear-phishing attacks that can have far-reaching implications on national security. An attack can expose classified information, jeopardizing national interests and potentially causing international incidents. In addition, our nation’s critical infrastructure, including energy grids, transportation networks, and healthcare systems, is at risk daily. A spear-phishing attack that compromises these agencies can have cascading effects on public services and safety, disrupting daily life and causing economic losses.

Examples of Real-Life Spear-Phishing Attacks
Historically, numerous high-profile entities have fallen victim to spear-phishing attacks, highlighting the severe implications of such breaches. For instance, a security company, RSA, suffered a massive data breach in 2011 due to a spear-phishing attack. In 2017, even tech giants like Google and Facebook were not immune, falling victim to an attack costing them over $100 million. Additionally, a notorious incident in 2016 led to the leakage of thousands of emails from the Democratic National Committee (DNC).

The Role of IT Operations and Support in Preventing Spear Phishing
Effective spear phishing defense necessitates robust IT operations and support. They must deploy advanced threat detection systems, utilizing machine learning to identify patterns indicative of spear phishing. Regular system updates, patching, and strict email policies are paramount to mitigate the risk of attacks.
Regular Backups and Incident Response
Data backups act as a safety measure in the event of successful attacks, enabling the restoration of systems and reducing potential damage. Moreover, a well-structured process for monitoring, detecting, and responding to spear phishing incidents is crucial to isolate affected systems and prevent future occurrences.
This process should include the following steps:
- Monitoring: IT operations and support should monitor network traffic, email, and other data for signs of a spear phishing attack. Various tools and techniques, such as advanced threat detection systems, can be employed to accomplish this.
- Detection: Once a potential spear phishing attack has been identified, IT operations and support should investigate whether it is legitimate. This may involve analyzing the email, checking the sender’s IP address, and contacting the sender to confirm that they sent it.
- Response: If a spear phishing attack is confirmed, IT operations and support should immediately isolate affected systems and prevent the attack from spreading. This may involve blocking the sender’s IP address, changing passwords, and restoring systems from backups.

Preventing Spear Phishing Attacks: Practical Steps
There are many practical steps that organizations can take to prevent spear phishing attacks. These include:
- Education: Employers should educate their employees about the dangers of spear phishing and how to identify and report suspicious emails. This education should be ongoing and tailored to employees’ specific roles and responsibilities.
- Multi-factor authentication (MFA): MFA increases the security of accounts by demanding that users provide multiple authentication factors, like a password and a code from a mobile device. It significantly heightens the difficulty for attackers trying to access accounts, even if they have managed to obtain a user’s password.
- Regular system updates: Software developers regularly release security patches to address vulnerabilities that attackers could exploit. By promptly applying these patches, organizations can help to reduce the risk of a successful spear phishing attack.
- Robust security policies: Organizations need strong security policies that encompass all aspects of IT security, including email security. It’s important to regularly review and update these policies to make sure they are effective against the newest threats.
In addition to these general measures, there are several other things that organizations can do to protect against spear phishing attacks, such as:
- Using spam filters: Spam filters can help to block phishing emails from reaching employees’ inboxes. However, it is essential to note that spam filters are imperfect, and some phishing emails may still get through.
- Reporting suspected phishing attempts: Employees should be encouraged to report suspicious emails to the IT department. This will help IT operations and support to investigate potential attacks and take steps to protect the organization.
- Being vigilant and suspicious: Employees should be alert and wary of unexpected emails, especially those that contain attachments or links. If an email looks suspicious, it is best to err on the side of caution and not click on any links or open any attachments.
Conclusion
In conclusion, spear phishing is a potent cyber threat, given its personalized and targeted nature. A multi-faceted approach involving technological measures, user education, and robust policies is crucial to safeguard sensitive information across various sectors. By staying informed and vigilant, individuals and organizations can fortify their defenses and mitigate the risks of spear-phishing attacks.
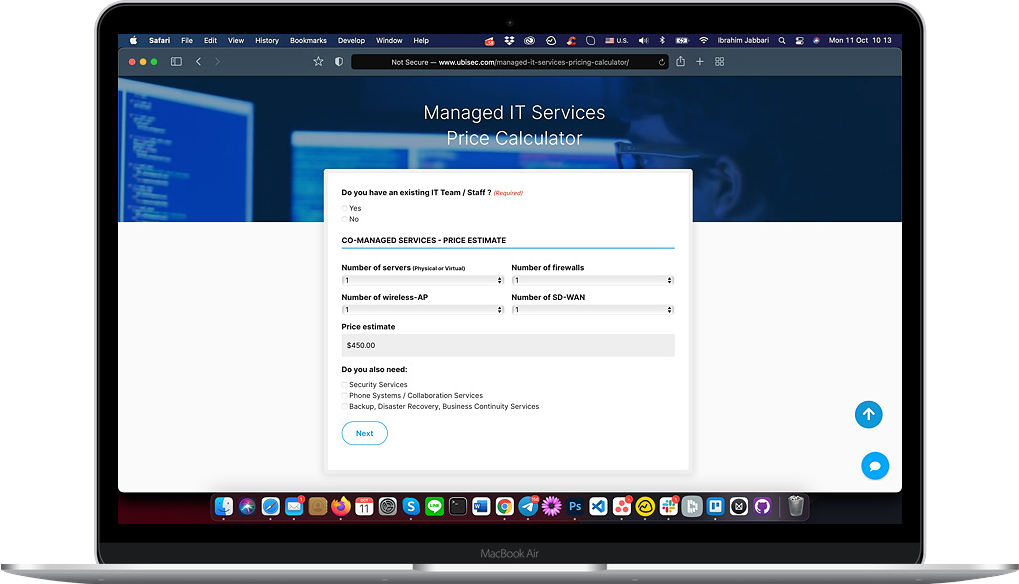
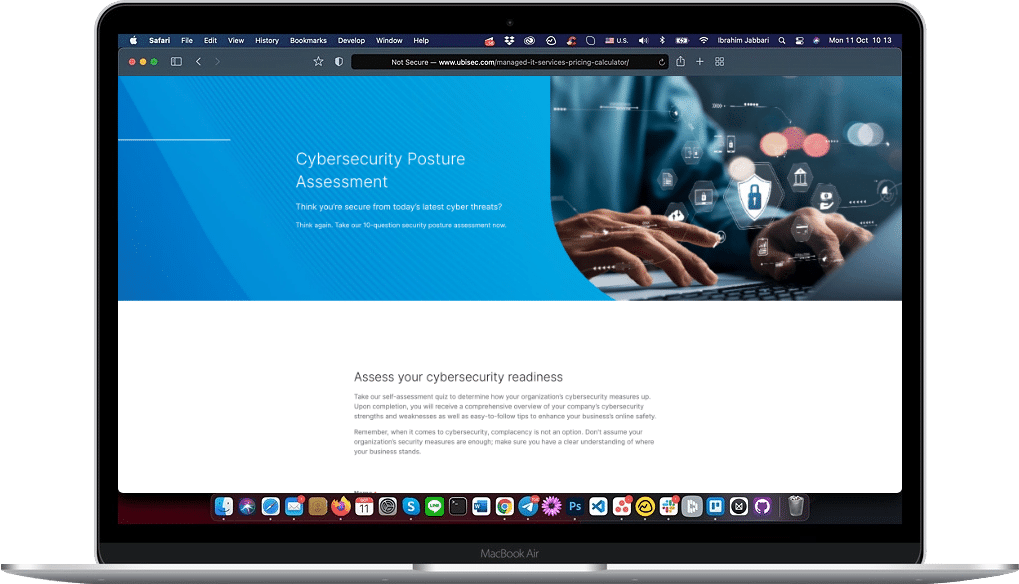
In fact, we’ve created a cybersecurity posture assessment quiz to help provide you with a comprehensive overview of your organization’s current security measures and some helpful recommendations. Click here to take the quiz.
Taking action is crucial to protect against spear phishing. One way to do that is by working with a cybersecurity expert like Ubisec Systems. We can help organizations stay safe from these tricky attacks.
Remember, spear phishing can lead to big problems, like losing important information and causing damage to a company’s reputation. So, to keep your info and your organization secure, consider teaming up with experts like us to defend against spear phishing.
Don’t hesitate to contact us here with any questions or need help with spear phishing protection. Stay safe in the digital world!
FAQs
What is spear phishing protection?
Spear phishing protection involves a combination of technology, policies, and user education to prevent unauthorized access to sensitive information through deceptive emails.
What is the risk of spear phishing?
The risk involves unauthorized access to sensitive information, financial losses, and potential damage to reputation and customer trust.
What are spear phishing examples?
Examples include the 2011 RSA data breach, the 2017 attack on Google and Facebook, and the 2016 DNC email leak.
Why is phishing challenging to prevent?
Its difficulty stems from the continually evolving tactics used by attackers and the human factor, where individuals may unknowingly fall for deceptive emails.
How do companies prevent phishing attacks?
Companies deploy advanced threat detection systems, enforce strict email and security policies, educate employees, and implement multi-layered security measures, including regular updates and patches.