Cybersecurity controls are integral to safeguarding systems, data, and people in today’s digital landscape. With the ever-increasing number and sophistication of cyber threats, organizations must prioritize implementing effective controls to mitigate risks and ensure their assets’ confidentiality, integrity, and availability. In addition, cybersecurity controls are crucial defenses against unauthorized access and malicious activities. They act as barriers, employing technologies like firewalls, intrusion detection systems, and access controls to monitor and regulate network traffic, detect suspicious activities, and enforce strict authentication measures. By implementing these controls, organizations significantly reduce the risk of successful cyber-attacks and protect their systems from unauthorized access and potential damage.
The Five Essential Security Controls
In today’s digital age, cybersecurity has become a critical concern for individuals and organizations. With the increasing sophistication of cyber threats, it’s essential to implement adequate security controls to protect sensitive information and systems.
Here are the five essential security controls that form the foundation of a robust cybersecurity strategy for your business:
Inventory and Control of Hardware Assets
One of the fundamental aspects of maintaining a secure environment is having a clear inventory and control of hardware assets. This control ensures that only authorized individuals can access sensitive information and systems. Organizations can effectively monitor and manage their infrastructure’s security by accurately identifying and documenting hardware assets.
Authentication methods play a crucial role in controlling access to hardware assets. Implementing robust authentication methods, such as multi-factor authentication (MFA), adds an additional layer of security to the authentication process. MFA requires users to supply multiple forms of identification, typically a combination of something they know (like a password), something they have (like a security token), or something they are (like a fingerprint). This approach significantly reduces the risk of unauthorized access, even if a password is compromised.
Another important principle in controlling hardware assets is the principle of least privilege. This principle states that users should have the minimum access necessary to perform their job functions. By following the principle of least privilege, organizations can limit the potential damage caused by unauthorized access or insider threats. Users’ access rights should be carefully reviewed and adjusted based on their job responsibilities and the principle of least privilege.
Having a precise inventory of hardware assets is crucial for effective security management. It allows organizations to identify and track all devices connected to their network, including servers, workstations, laptops, mobile devices, and networking equipment. This inventory helps identify unauthorized or rogue devices that pose a security risk. Maintaining an up-to-date inventory also enables organizations to promptly apply necessary security patches and updates to all hardware assets, reducing vulnerabilities.
Furthermore, inventory management facilitates proactive planning and response during hardware failures or security breaches. With a comprehensive inventory, organizations can quickly assess the impact of such incidents, identify affected assets, and take appropriate measures to mitigate risks and restore operations efficiently.
Inventory and Control of Software Assets
Organizations rely heavily on software to support their operations and deliver services in today’s interconnected world. However, with the increasing number of software vulnerabilities and cyber threats, it is crucial to have proper inventory and control of software assets to protect the organization’s network infrastructure from unauthorized access and attacks.
Applying robust security measures, such as firewalls, intrusion detection systems (IDS), and intrusion prevention systems (IPS), helps safeguard the organization’s network. Firewalls are a barrier between internal and external networks, monitoring and controlling incoming and outgoing traffic. IDS and IPS detect and prevent unauthorized access attempts and malicious activities, providing an additional defense against cyber threats.
Another critical aspect of software asset control is ensuring secure communication between external parties. Encryption techniques and secure protocols, such as SSL/TLS, help establish secure channels for data transmission and protect sensitive information from interception and unauthorized access. By encrypting sensitive data, organizations can ensure the confidentiality and integrity of their communications.
Continuous Vulnerability Management
The confidentiality, integrity, and accessibility of an organization’s data are critical for its operations and reputation. Continuous vulnerability management is vital in identifying and addressing vulnerabilities to protect the organization’s assets.
Encryption, data classification, and data loss prevention (DLP) technologies are critical elements of vulnerability management. Encryption converts data into unreadable form, making it inaccessible to unauthorized individuals. Data classification involves categorizing data based on its sensitivity, allowing organizations to implement appropriate security controls based on the classification. DLP technologies help prevent the unauthorized disclosure of sensitive data by monitoring and controlling its flow within the organization.
Regular data backups ensure data availability and resilience against potential data loss incidents. Organizations can quickly recover from data breaches, hardware failures, or natural disasters by maintaining up-to-date backups. Developing a robust disaster recovery plan also enables organizations to minimize downtime and resume operations promptly during a disruption.
Controlled Use of Administrative Privileges
Employees are often a vulnerability point in an organization’s cybersecurity defenses. Educating employees about cybersecurity and their role in protecting the organization’s assets is crucial for maintaining a secure environment.
Regular training and awareness programs help employees stay informed about the latest threats and security best practices. By keeping employees up-to-date, organizations can empower them to identify and respond appropriately to potential security risks. Encouraging a security culture within the organization fosters a proactive approach toward cybersecurity, with employees actively safeguarding sensitive information and systems.
Monitoring for the misuse of administrative privileges is another vital control. Administrative privileges provide individuals with elevated access and control over systems and data. However, if these privileges are misused or compromised, they can pose a major risk to the organization. Implementing monitoring mechanisms, such as audit logs and access controls, helps in identifying any unauthorized or suspicious activities related to administrative privileges, enabling prompt intervention and mitigation of potential threats.
Secure Configuration for Hardware and Software
Preparing for security incidents and having a well-defined incident response plan is crucial for minimizing the impact of such events. Secure configuration for hardware and software is an essential control in this regard.
Developing an incident response plan involves defining roles and responsibilities, establishing communication protocols, and outlining recovery procedures. This plan provides clear guidance on responding to and recovering from security incidents effectively. Regular testing and updating of the plan ensure its effectiveness and alignment with the evolving threat landscape.
Addressing security incidents requires a coordinated and organized approach. By following the incident response plan, organizations can quickly contain and mitigate the impact of an incident, minimizing potential damage and downtime. Additionally, thorough post-incident analysis helps identify lessons learned and areas for improvement, enhancing the organization’s overall security posture.
Conclusion
In conclusion, implementing cybersecurity controls is essential for organizations to protect their systems, data, and people from cyber threats. These controls act as vital defenses, preventing unauthorized access and malicious activities. They include firewalls, intrusion detection systems, and access controls that monitor and regulate network traffic, detect suspicious activities, and enforce strict authentication mechanisms. By establishing these controls, organizations significantly reduce the risk of cyber-attacks and safeguard their systems.
Furthermore, cybersecurity controls are crucial in securing data and ensuring its integrity. Encryption, data classification, and loss prevention technologies protect data at rest, in transit, and in use. Encryption transforms data into an unreadable format, while data classification enables the application of appropriate security controls. Data loss prevention technologies monitor data flow to prevent unauthorized disclosure. These controls establish a robust data protection framework, safeguarding critical information from unauthorized access or alteration.
Cybersecurity controls also prioritize the safety of individuals by raising awareness and implementing practices to combat threats. Training programs educate employees about cybersecurity best practices, multi-factor authentication adds an additional layer of protection, and secure browsing practices minimize the risk of falling victim to attacks. Organizations can create a safer online environment for their employees, customers, and partners by empowering individuals.
Finally, cybersecurity controls are vital for organizations in today’s digital landscape. They protect systems, data, and people from cyber threats by establishing barriers, securing data, and promoting a security culture. By investing in these controls, organizations can mitigate risks, maintain the confidentiality and integrity of their assets, and safeguard against potential cyber-attacks. Prioritizing cybersecurity controls is a proactive step toward protecting sensitive information and maintaining stakeholder trust in an increasingly interconnected world.
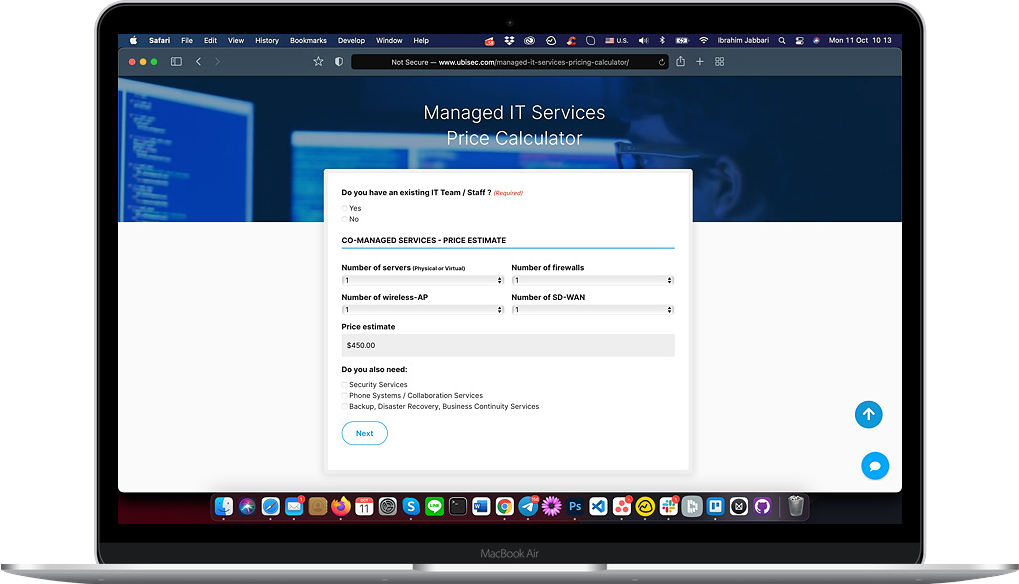
We here at Ubisec Systems recognize the essential need for data security and peace of mind over protecting your digital assets. We’d love to start a conversation with you and if you’re ready, click here to start NOW!